Cars are more complex than ever, with all the technology crammed into a single chassis. The greatest feat is that a modern automobile is a masterpiece of our connected environment. Every day we never even comprehend that enhanced connectivity is around us and an integral part of the digital age. In the depths of cyber-space lurks hackers that are a constant threat.
Utilizing the digital cloud connects the cars digital environment and wireless protocols that improve automobile functions. All this connectivity is akin to swiss cheese because all the holes are vulnerabilities that are a source of digital attacks. Connectivity is good, but there's a price to pay for it. Those in the depths of the internet are learning to bypass and exploit the system without notice.
With more car companies trying to up the ante in infotainment and digital connectivity in the shortest period. Straining the cars digital environment that is not very optimal. Despite the sophistication of the technology, there are limits to how secure car networks are, manufacturing these components, and how these systems handle well automotive data. Connectivity and improving it is causing problems that consumers don't realize is a detriment to the security of their vehicle's network. To be specific, these issues are problematic, and desire for more integrated digital systems connecting with personal devices and remote access is an Achilles heel. This observation is put forward by industry experts who are greatly concerned with this development that involves improved connectivity.
Hackers are adept at hitting digital vehicle systems with more than one way to get it done. Motorists aren't even aware that their vehicle can be hacked with the greatest of ease. All the security flaws are continually changing, and it's like a cat and mouse game.
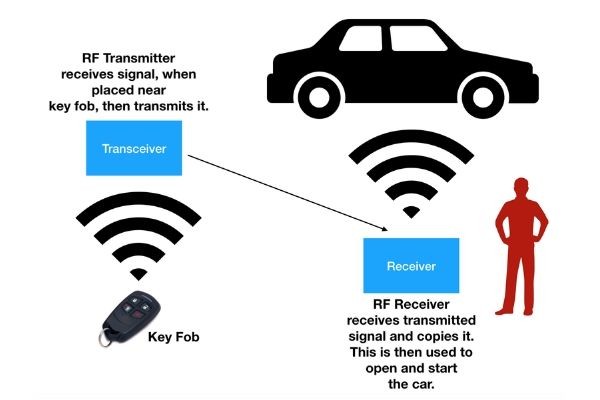
This is the easiest wherein the signal is cloned by a receiver and sent to a device to open a car. This is the simplest, yet most vulnerable way to get a car opened.
2. Tire pressure monitoring systems
Messages via the TPMS will be hacked via radio forcing the driver to make a stop.
The controller area network is hacked by external sources or programs that are installed without the knowledge of the owner. Examples are updates to the OS or even intentional uploading in the dealership.
4. GPS spoofing
GPS data is manipulated by hackers to give the wrong information using a radio transmitter.
5. Mobile service attacks
When personal devices connect with the infotainment, this is when the system is hacked. Mobile connectivity is another avenue and a problem for car network security.
Keeping tabs on security risks and recognizing them. When they rear their ugly heads is an immediate concern. Most motorists aren't aware, but their cars are like a duck in a shooting gallery with enhanced connectivity in their vehicles. Mobiles and other personal devices are their gateways into the system. This is often ignored and not taken heed off, which is quite well for hackers.
Cars are more complex than ever, with all the technology crammed into a single chassis. The greatest feat is that a modern automobile is a masterpiece of our connected environment. Every day we never even comprehend that enhanced connectivity is around us and an integral part of the digital age. In the depths of cyber-space lurks hackers that are a constant threat.
See Now: OnePlus 6: How Different Will It Be From OnePlus 5?


























